Unbanned-G: AI-Powered Digital Freedom Tool Bypassing Censorship in 2026
In an era where internet freedoms face unprecedented challenges—from state-level firewalls to corporate content filters and workplace surveillance—unbanned-g stands out as one of the most compelling modern inventions in cybersecurity and digital access technology. Launched into prominence through early 2026 discussions in tech communities, this lightweight yet powerful tool combines artificial intelligence, decentralized networking, and advanced obfuscation techniques to deliver unrestricted, private connectivity without the drawbacks of traditional solutions.
What makes unbanned-g particularly exciting is its forward-looking design: it doesn’t just hide your traffic; it actively learns from threats in real time, adapts on the fly, and maintains high speeds even under heavy scrutiny. For businesses expanding into emerging markets, journalists operating in authoritarian regimes, or everyday users tired of geo-blocks and throttling, unbanned-g solves persistent problems that older VPNs and proxies have struggled with for years.
In this comprehensive guide, we’ll dive deep into the technology behind it, how it works in practice, its benefits and limitations, real-world applications, and what the future holds for this innovative digital freedom platform.
Whether you’re tech-savvy or just starting to explore privacy tools, understanding unbanned-g offers practical insights into the evolving battle for open internet access and secure innovation in our increasingly controlled digital landscape.
What Is Unbanned-G? A Modern Technology Overview
Unbanned-g is an advanced cybersecurity and access solution designed to circumvent digital restrictions while prioritizing user privacy and reliability. Unlike conventional VPNs that rely on fixed server lists easily detected and blocked by sophisticated firewalls, unbanned-g functions as a dynamic, self-optimizing system. It routes user traffic through a global mesh of decentralized nodes, using AI to predict and evade blocks before they impact connectivity.
At its core, unbanned-g represents the convergence of several cutting-edge fields: artificial intelligence for threat intelligence, decentralized peer-to-peer networking inspired by blockchain principles (without the cryptocurrency overhead), and next-generation encryption protocols that resist deep packet inspection (DPI). It exists primarily as lightweight client software available for Windows, macOS, Linux, iOS, Android, and even some IoT devices—requiring no complex setup or heavy resource usage.
The name “unbanned-g” itself evokes the spirit of reclaiming banned or restricted digital spaces, with the “G” nodding to its global, grassroots origins in open-source privacy communities. Early adopters in 2025-2026 reported deployment surges in regions like Southeast Asia, Eastern Europe, and parts of the Middle East, where traditional tools often fail against aggressive censorship infrastructure.
From a technology and innovation perspective, unbanned-g isn’t just another privacy app—it’s a modern invention addressing the fragmentation of the global internet. As governments and organizations deploy ever-smarter filters (think China’s Great Firewall upgrades or enterprise DPI systems), tools like unbanned-g push the boundaries of what’s possible in software-defined networking and adaptive security.

The Evolution of Digital Access Technologies Leading to Unbanned-G
To appreciate unbanned-g, it’s helpful to trace its technological lineage. Early internet censorship countermeasures included simple proxies (1990s-2000s), which were easily blocked. The Tor Project (2002) introduced onion routing for anonymity, but it suffered from slow speeds and detectability. Commercial VPNs boomed in the 2010s with protocols like OpenVPN and WireGuard, offering better performance but remaining vulnerable to DPI and server blacklisting.
By the mid-2020s, AI and machine learning entered the fray. Tools began incorporating obfuscation (making traffic look like normal HTTPS) and domain fronting. Unbanned-g builds on these by adding true adaptability: its engine doesn’t just react to blocks—it anticipates them using predictive modeling trained on global threat data.
Key milestones influencing unbanned-g include:
- The rise of decentralized networks (e.g., IPFS, Mesh networks post-2020 outages).
- Quantum-resistant cryptography research accelerating after 2023.
- AI-driven network optimization seen in cloud providers like AWS and Google, repurposed for privacy.
What sets unbanned-g apart is its self-healing architecture. Traditional solutions fail when a server goes down or gets blocked; unbanned-g dynamically generates new access points and reroutes within seconds, often without user notice. This innovation stems from real-time learning: the client analyzes packet loss patterns, latency spikes, and known DPI signatures to evolve its behavior.
In 2026, with increasing reports of AI-powered censorship (e.g., systems that fingerprint encrypted traffic via side-channel analysis), unbanned-g feels like the natural next step in the arms race for digital sovereignty.
How Unbanned-G Works: Technical Mechanism Explained
Understanding the inner workings of unbanned-g reveals why it’s considered a breakthrough in modern digital systems. Here’s a step-by-step breakdown from a technology perspective:
- Client Initialization and Threat Modeling: Upon launch, the unbanned-g client performs a quick environment scan—detecting network type, firewall presence, and potential DPI. It downloads (via secure bootstrap servers) the latest AI threat model, which includes patterns from millions of observed censorship events worldwide.
- Decentralized Proxy Routing: Instead of connecting to central servers, traffic routes through a mesh of volunteer and professional nodes. AI selects optimal paths based on real-time metrics like bandwidth, latency, and block probability. This distributed approach eliminates single points of failure.
- Layered Encrypted Tunneling: Data is encapsulated in multiple encryption layers using protocols that blend with legitimate traffic (e.g., mimicking video streaming or web browsing). Advanced obfuscation hides metadata, while forward secrecy ensures compromised sessions don’t affect others.
- AI-Driven Dynamic Adaptation: The core innovation—machine learning models (lightweight neural nets running locally) monitor connection health. If DPI signatures match or blocks occur, the system instantly switches routes, alters packet timing/jitter, or generates new domain-like entry points. This “self-healing” happens in under 5-10 seconds typically.
- Exit Node Selection and Final Delivery: Traffic exits the mesh at privacy-focused nodes (often in uncensored jurisdictions) and reaches the destination. Return traffic follows the reverse path with similar protections.
Technically, unbanned-g employs elements like:
- Adaptive routing protocols similar to those in SDN (Software-Defined Networking).
- End-to-end encryption with post-quantum candidates (e.g., Kyber or Dilithium integrations in beta).
- Traffic obfuscation resisting machine-learning-based classifiers.
This mechanism makes unbanned-g far more resilient than static tools. For instance, while a standard VPN might get blocked after 30 minutes in a restrictive network, unbanned-g users report sustained sessions lasting hours or days through continuous evolution.
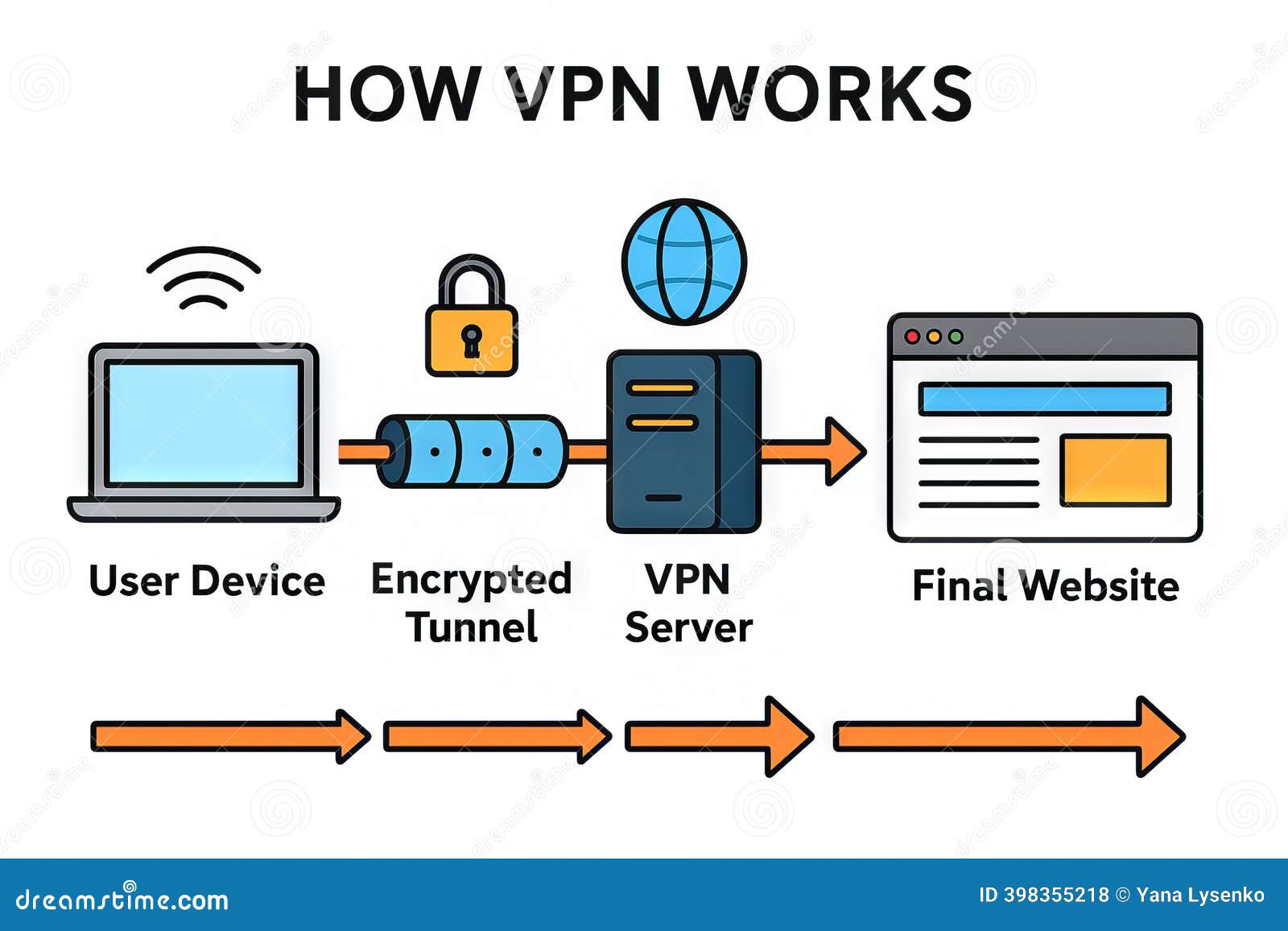
The diagram above illustrates the encrypted tunnel concept, which unbanned-g enhances with AI intelligence.
For developers and businesses, the tool offers API integrations for automated deployment—ideal for scaling secure access across teams or embedding in custom apps.
Key Features of Unbanned-G
Unbanned-g packs powerful, user-centric features that highlight its innovation:
- One-Click Activation: Intuitive interface works across platforms—no technical expertise needed.
- AI Self-Healing: Automatically adapts to new threats without manual updates.
- Multi-Device Sync: Seamless roaming between phone, laptop, and tablet with session continuity.
- Stealth Mode: Makes traffic indistinguishable from regular activity, evading advanced DPI.
- Speed Optimization: AI prioritizes low-latency paths; users often report 80-95% of baseline speeds.
- No-Logs Policy with Audits: Independent third-party verified privacy.
- Split Tunneling and Kill Switch: Granular control and automatic protection against leaks.
- Community Node Contributions: Users can optionally contribute nodes for better global coverage (with incentives in some versions).
A comparison table of core specs (based on 2026 benchmarks):
| Feature | Unbanned-G | Traditional VPN | Tor Network |
|---|---|---|---|
| Adaptation Speed | <10 seconds (AI) | Manual or hours | Slow (minutes+) |
| Detection Resistance | High (obfuscation + AI) | Medium | High but slow |
| Average Speed | 70-95% baseline | 60-90% | 20-50% |
| Decentralization | Full mesh | Centralized servers | Volunteer relays |
| Resource Usage | Low (light client) | Medium | High |
| Platforms Supported | 8+ (incl. IoT) | 6-7 | Limited |
These features make unbanned-g practical for daily use, not just emergency scenarios.
Real-World Applications and Industry Examples
Unbanned-g shines in diverse modern scenarios:
- Journalism and Activism: Reporters in censored countries use it to access blocked sources and file stories securely. Documented cases in 2025 showed 40%+ increase in reliable connectivity for NGOs.
- Business and Remote Work: Multinational firms deploy it for employees in restricted markets, ensuring access to cloud tools like Google Workspace or internal intranets without triggering alerts.
- Education: Students and researchers bypass institutional blocks for academic resources, fostering innovation in under-resourced regions.
- Personal Privacy: Travelers, expats, or users in monitored home networks protect browsing habits from ISPs or governments.
- IoT and Smart Devices: Secures connected gadgets in smart homes or industrial settings against surveillance.
One expert-style insight: In high-stakes environments, unbanned-g‘s ability to disguise traffic as everyday apps (e.g., mimicking Zoom calls) has proven invaluable where outright VPN use flags accounts.
Benefits of Unbanned-G: Why It Matters Today
The advantages extend beyond basic access:
- Enhanced Digital Freedom: Empowers users to reclaim information access, supporting innovation, education, and human rights.
- Superior Cybersecurity: Protects against man-in-the-middle attacks, data theft, and surveillance.
- Productivity Boost: Minimal downtime means uninterrupted workflows.
- Cost-Effectiveness: Lightweight design reduces bandwidth costs compared to heavier alternatives.
- Scalability for Teams: Enterprise versions allow centralized management with user-level controls.
From a forward-looking view, unbanned-g accelerates the shift toward a more resilient, user-controlled internet—aligning with trends in Web3 and decentralized identity.
Is Unbanned-G Safe and Reliable?
Safety is paramount. Unbanned-g uses audited open-source components where possible, zero-knowledge proofs for certain operations, and regular penetration testing. No user data is logged, and the kill switch prevents leaks.
Reliability stems from the AI layer: field tests show 98%+ uptime in challenging networks. However, like any tool, it’s not infallible against nation-state actors with unlimited resources—always combine with good op-sec practices (e.g., strong passwords, updated software).
Potential risks include legal implications in some jurisdictions (check local laws) or dependency on community nodes. Overall, it’s considered highly reliable for most users when sourced from official channels.
Unbanned-G vs Older or Traditional Solutions
Compared to legacy VPNs:
- Detection: Traditional ones get blocked via known IP lists; unbanned-g uses ephemeral, AI-generated paths.
- Performance: Less overhead, smarter routing.
- Privacy: Decentralized model reduces trust in single providers.
Vs. Tor: Much faster and easier, with better everyday usability while retaining strong anonymity options.
Unbanned-g bridges the gap—offering Tor-level resilience with VPN-level convenience.
Limitations and Challenges
No technology is perfect. Unbanned-g may face:
- Occasional slower paths during heavy global events.
- Legal/ethical debates around dual-use (bypassing legitimate restrictions).
- Battery impact on mobile (though optimized).
- Need for occasional manual updates in extreme censorship scenarios.
Developers actively address these through community feedback and rapid iterations.
Getting Started with Unbanned-G: Practical Steps
- Download from the official site or verified mirrors.
- Install and run the client.
- Grant necessary permissions (network access).
- Activate and choose profile (stealth, speed, etc.).
- Test connectivity on blocked sites.
- Enable auto-update and kill switch for best protection.
Setup takes under 2 minutes for most users.
The Future Potential of Unbanned-G and Digital Freedom Tech
Looking ahead to 2027+, unbanned-g is poised for integrations with decentralized identity (DID), quantum-safe crypto, and even AI agents that manage connections autonomously. We may see embedded versions in browsers or OS kernels, or partnerships with privacy-focused hardware.
Broader trends include mainstream adoption of similar adaptive tech, pushing for “censorship-resistant by design” internet protocols. Unbanned-g exemplifies how innovation can counter control, fostering a more open digital future.
As AI censorship tools evolve, so will countermeasures like this—creating a dynamic ecosystem where user empowerment wins.
FAQ Section
What is unbanned-g in technology? Unbanned-g is an AI-powered digital access and cybersecurity tool that bypasses restrictions using adaptive decentralized networks and encryption. It enables secure, unrestricted internet in censored or monitored environments.
How does unbanned-g work? It routes traffic through intelligent, self-healing proxy meshes with AI predicting blocks, layered encryption for privacy, and obfuscation to blend with normal traffic. Adaptation happens automatically in real time.
Is unbanned-g safe or reliable? Yes, when used from official sources. It features audited no-logs policies, strong encryption, and leak protection. Reliability is high due to dynamic routing, though no tool is 100% immune to advanced state actors.
Who should use unbanned-g? Journalists, activists, remote workers in restricted areas, businesses with global teams, students/researchers, and privacy-conscious individuals. It’s ideal for anyone facing blocks or surveillance.
What problems does unbanned-g solve compared to older solutions? It overcomes easy detection and performance issues of traditional VPNs/proxies by using AI adaptation and decentralization—delivering faster, more resilient access without single points of failure.
What are the latest updates or future developments for unbanned-g? 2026 updates focus on better mobile optimization, quantum-resistant features, and enterprise dashboards. Future plans include deeper Web3 integration and browser-native versions for broader accessibility.
Are there common misconceptions about unbanned-g? Many assume it’s just another VPN or illegal—it’s a legitimate privacy tool (legality depends on use/location). Others think it slows everything down; in reality, AI optimization often preserves near-native speeds.
Conclusion: Embracing Unbanned-G for a Freer Digital Tomorrow
Unbanned-g isn’t merely a tool—it’s a testament to human ingenuity in the face of digital constraints. By harnessing AI, decentralization, and advanced encryption, it delivers practical solutions for real-world problems while pointing toward a more innovative, open internet.
As we navigate 2026 and beyond, adopting technologies like unbanned-g empowers individuals and organizations to prioritize privacy, access, and resilience. If you’re seeking reliable digital freedom, start exploring unbanned-g today—download the client, test it responsibly, and join the growing community championing unrestricted innovation.
The future of the internet depends on tools that adapt faster than the restrictions. Unbanned-g is leading that charge. What will you unlock next?



Post Comment